The first thing we need to remember that any Operating System has been created by people - who are prone to make mistakes no matter how careful they are, it's just the human condition.
Another thing to take into consideration is the amount of code that has been written just to create these Operating Systems. As an example, there were approximately 45 million lines of code that were used to compile Windows XP and around 86 million lines of code to create Mac OS X 10.4. I don't know about you but that is more than I can imagine.
This means that Operating Systems are really, really complex. Even though they make what they do look simple.
Next, we find that the vendors - Microsoft, Apple, etc are always making changes to this code to remove security holes that have been found by researchers, anti-virus vendors and hackers. This is why there is always a stream of updates coming from Apple / Microsoft and all the other Operating System vendors.
At the time of writing this post, Apple currently have approximately 10% of the market place and Windows has around 60%.
It makes more sense for the malware creators to target the Operating System that has the largest market share.
If the numbers were reversed and Apple had the majority, this article would be titled "Are Windows computers safe from malware infections?"
Because Microsoft has the larger percentage of end users, that is why the hackers target them. Or, to put it another way, why would you try to exploit the smaller number of computers when you can exploit a larger number of computers and make more money?
With that said, there are a number of malware programs that have been created that are cross platform (they will run on any platform) or they run on an application like Oracle's Java or Adobe Reader. Which is why there have been numerous updates to these programs and others to address the security holes and improve security in general.
So malware is here to stay and in the future will be more creative, while the Operating System / application vendors work hard to reduce the number of security holes in their products. Plus the Anti-Virus vendors work to find ways to detect and repel the malware' before they can get into your systems.
Conclusion: It makes no difference what the operating system is, or who created it. They all have security holes in them that can and will be exploited by the malware creators. Just because Mac OS-X doesn't appear to be affected by malware does not mean that there is no malware created for it and as time goes on there will be more created for the Apple platform.
My recommendations:
- No matter what Operating System you are running, it is important to install a good anti-virus product (for Mac OS-X we recommend ESET Cybersecurity)
- Remove any programs that you don't use from your computer. That way you reduce the ability of malware to get into your computer.
- Be paranoid about the web sites that you visit and the software that they want you to install.
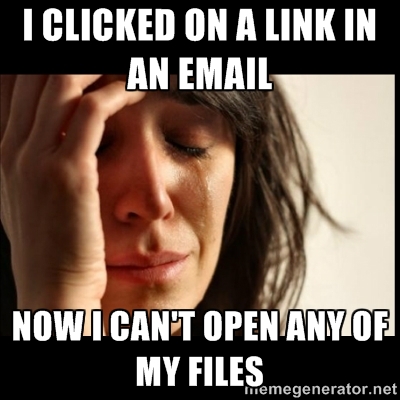
- Also be paranoid about your email and never open an attachment, unless you are expecting to receive it.
- Don't click on any links in email, unless you are expecting something (like a link to reset your password). You're mostly safer by typing the address into a web browser that clicking on a link.
- Last, but not least - Banks will never send you email that has a link that you must follow. Instead, always type your banks URL into the address bar of your web browser, never ever click on a link in an email.